FvncBot malware found can trap user typing
FvncBot malware found, can trap the printing of Android users and install more malware.
It seems that the mobility of Android is required at the expense of the risk of use, because the system is open to a variety of developers, so that hackers are "involved" in creating malware that happens, creating fear with users every day, as in this news.
According to a report by the GB website, Hackers has mentioned the detection of a malware distribution campaign of a suction type from a bank account, or a new Banking Trojan called FvncBot. This malware will focus its attacks on a group of mobile phone users on the Android operating system, which was detected by a research team from Intel 471, a cybersecurity expert organization. The research team found that the malware was detected last November in which the malware was exploded in Poland by impersonating an application of the famous bank mbank in Poland under the package "."
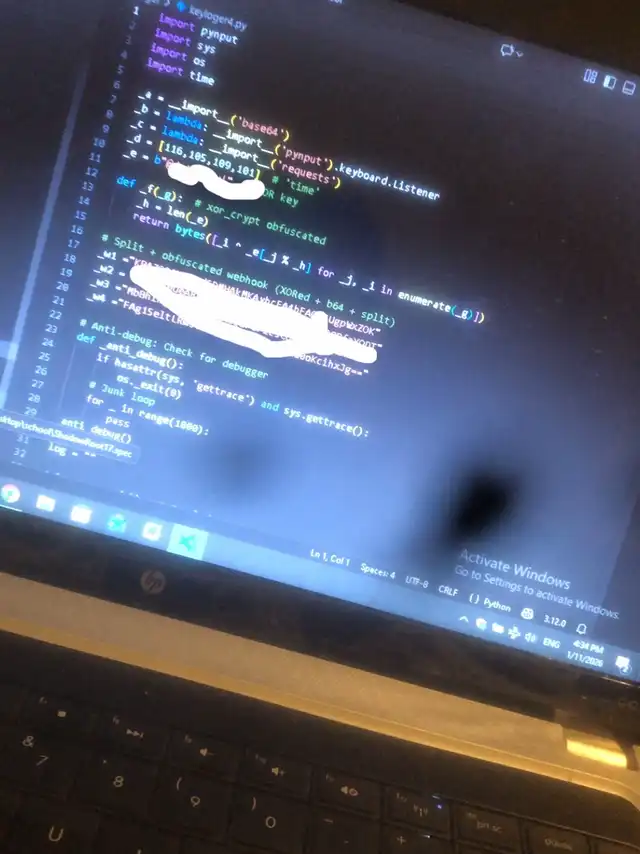
For technical data, the research team revealed that the FvncBot malware, which has been detected as a completely rewritten malware, does not rely on source code from the same type of malware that is popular with other malware developer hackers such as Ermac or Hook. In any way, embedded on the victim's machine is divided into two steps:
The first step is to use a fake application as a malware extension, or a Loader that claims to be an element of Google Play (Play Component) that will allow for safer and more stable use of bank applications.
The second step, after the installation is completed, the Loader will unpack the real payload files hidden within the assets of the fake application on the victim's machine.
These two components have been used as an apk0day Crypting Service to confuse the Obfuscation, allowing it to emanate on the victim's machine.
After the malware has been embedded on the victim's machine, the malware will request a Permission to access the Accessibility Mode to be used to trap the victim's typing (Keylogging). This capture is intended to steal the victim's password and sensitive information, focusing on financial information. The data collected will be stored in a Buffer memory section that can store up to 1,000 pieces of data before sending the hacker through the HTTP Request to the C2 control server or Command. And Control)
In addition, the malware is used to overlay the screen. By using WebView with the web-Injection Attacks, JavaScript is used when the victim is opening the bank application. Instead of the victim actually entering the bank app, the display on the secret grail shows a deception screen similar to the app that was opened with WebView instead to deceive the bank application password. The list of applications aimed by the malware and the URL of the phishing web display is downloaded from the C2 server and stored on the machine.
Not only that, malware also has many capabilities, including opening a channel for hackers to take control of the machine through the Web Socket. This allows hackers to scroll, click, swipe the screen freely, or even open applications to fill in the data themselves, even taking control of the data on the Clipboard. And even worse, hackers can create black screens to cover their own activities, mute or even log the victim's machine. They can also stream the screen to hackers through the MediaProjection API with the use of Codec H.264 Video Encoding.
Moreover, to make it more convenient for hackers, the malware also has a Text Mode implementation through the Virtual Network Computing (VNC) function, which stores the structure of the display on the screen through the Accessibility Mode. Recontruction is not necessary to use Screenshot.
# Welcome 2026 # Take care of yourself # Open budget # Includes IT matters # Trending